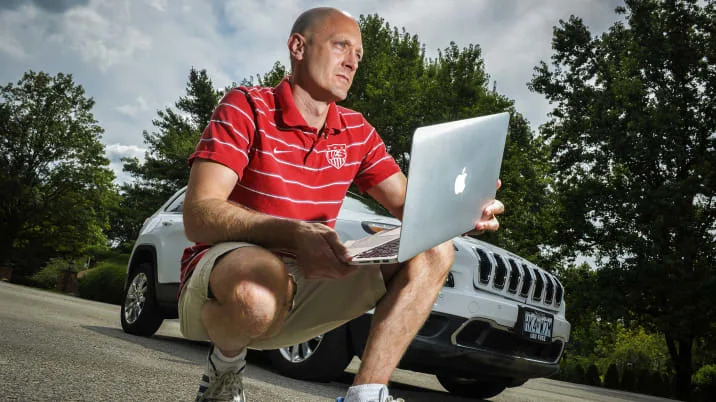
More than anyone, Chris Valasek and Charlie Miller are responsible for alerting Americans to the hacking perils awaiting them in their modern-day cars.
In 2013, the pair of cyber-security researchers followed in the footsteps of academics at the University of Cal-San Diego and University of Washington, demonstrating it was possible to hack and control cars. Last summer, their research established which vehicles contained inherent security weaknesses. In recent weeks, their latest findings have underscored the far-reaching danger of automotive security breaches.
From the comfort of his Pittsburgh home, Valasek exploited a flaw in the cellular connection of a Jeep Cherokee and commandeered control as Miller drove along a St. Louis highway. Remote access. No prior tampering with the vehicle. An industry's nightmare. As a result of their work, FCA US recalled 1.4 million cars, improving safety for millions of motorists.
For now, Valasek and Miller are at the forefront of their profession. In a few months, they could be out of jobs.
Rather than embrace the skills of software and security experts in confronting the unforeseen downside of connectivity in cars, automakers have been doing their best to stifle independent cyber-security research. Lost in the analysis of the Jeep Cherokee vulnerabilities is the possibility this could be the last study of its kind.
In September or October, the U.S. Copyright Office will issue a key ruling that could prevent third-party researchers like Valasek and Miller from accessing the components they need to conduct experiments on vehicles. Researchers have asked for an exemption in the Digital Millennial Copyright Act that would preserve their right to analyze cars, but automakers have opposed that exemption, claiming the software that runs almost every conceivable vehicle function is proprietary.
Further, their attorneys have argued the complexity of the software has evolved to a point where safety and security risks arise when third parties start monkeying with the code. Their message on cyber security is, as it has been for years, that they know their products better than anyone else and that it's dangerous for others to meddle with them.
But in precise terms, the Jeep Cherokee problems show this is not the case. Valasek and Miller discovered the problem, a security hole in the Sprint cellular connection to the UConnect infotainment system, not industry insiders. This is only the latest example of independent researchers finding flaws that catch the industry by surprise. Third-party researchers at Cal-San Diego and Washington were the first to show automakers there were cyber holes in their cars. Third-party researchers were the ones who found vulnerabilities in the Progressive Insurance "Snapshot" dongle. Now FCA's UConnect system.
Hopefully, Copyright Office officials have noted those distinctions. They're important ones, because industry officials have bristled at independent researchers both during and after May hearings on the copyright law. In a summary of a letter sent earlier this month to a Congressional committee investigating car hacking, the Auto Alliance, the industry's leading trade group, likened them to "technology pirates."
"Automakers are facing pressure from the organized efforts of technology pirates and anti-copyright groups to allow the circumvention of protection onboard networks, and to provide hackers with the right to attack vehicles carte blanche under the auspices of research," the Alliance wrote. Publicizing research results is another aspect of independent research that automakers oppose. They equate it to providing a blueprint for malicious hackers.
But at the same time, automakers have ignored past results when researchers withheld details of their work. While noting they withheld key details from their work to prevent a criminal copycat from following their trail, Valasek lamented such a lose-pose proposition. "If you don't show everyone your hand of cards, people dismiss it or question the actual research or results," said Valasek, director of vehicle security at IOActive. "So the best thing to do is get in the car and show them how it works, and hopefully cars become more secure after this."
More importantly, the public scrutiny of the results has ensured vulnerabilities get fixed. Would cars have been secured if independent researchers had been prohibited from doing their work? Probably not. In FCA's case, the company didn't even know about the vulnerabilities until Valasek and Miller alerted them back in October.

When the company held a conference call with federal safety officials on July 16, they merely intended to issue a technical service bulletin to advise dealers on how to fix the problem, according to a chronology of events filed with the National Highway Traffic Safety Administration. But when WIRED Magazine ran a story explaining the hack on July 21, federal officials took immediate notice. Under pressure from the government, FCA issued a recall two days later.
"The Homeland Security folks sent out broadcasts that, "Here's an issue that needs to be addressed," said Nathaniel Beuse, associate administrator at NHTSA. Elsewhere, Senators Ed Markey (D-MA) and Richard Blumenthal (D-CT) have introduced legislation to set minimum federal standards for automotive technology and have since urged NHTSA to investigate whether more recalls are needed.
None of that happens without Valasek and Miller's research.
A ruling from the Copyright Office may come in September or October. Should the Office permit the work of third-party researchers to continue, industry leaders have indicated they may take their fight against independent researchers to Congress.
In the meantime, they continue to downplay the valuable role of independent search. Earlier this month, when the industry announced the creation of a Information and Sharing Analysis Center that will evaluate cyber threats, an official emphasized they wanted to work with researchers in "controlled environments," which was a nice way of saying researchers willing to keep their results secret.
Five years into the hacking threat, automakers still don't get it. They're still months away from getting the ISAC operational and still more concerned about being embarrassed by security flaws than actually getting them fixed. In confronting a challenge they've proven ill-equipped to address, they're intent on chasing the best hopes they've got at solving the problem right out of the discussion.
Related Video:
In 2013, the pair of cyber-security researchers followed in the footsteps of academics at the University of Cal-San Diego and University of Washington, demonstrating it was possible to hack and control cars. Last summer, their research established which vehicles contained inherent security weaknesses. In recent weeks, their latest findings have underscored the far-reaching danger of automotive security breaches.
From the comfort of his Pittsburgh home, Valasek exploited a flaw in the cellular connection of a Jeep Cherokee and commandeered control as Miller drove along a St. Louis highway. Remote access. No prior tampering with the vehicle. An industry's nightmare. As a result of their work, FCA US recalled 1.4 million cars, improving safety for millions of motorists.
For now, Valasek and Miller are at the forefront of their profession. In a few months, they could be out of jobs.
Rather than embrace the skills of software and security experts in confronting the unforeseen downside of connectivity in cars, automakers have been doing their best to stifle independent cyber-security research. Lost in the analysis of the Jeep Cherokee vulnerabilities is the possibility this could be the last study of its kind.
In September or October, the U.S. Copyright Office will issue a key ruling that could prevent third-party researchers like Valasek and Miller from accessing the components they need to conduct experiments on vehicles. Researchers have asked for an exemption in the Digital Millennial Copyright Act that would preserve their right to analyze cars, but automakers have opposed that exemption, claiming the software that runs almost every conceivable vehicle function is proprietary.
Further, their attorneys have argued the complexity of the software has evolved to a point where safety and security risks arise when third parties start monkeying with the code. Their message on cyber security is, as it has been for years, that they know their products better than anyone else and that it's dangerous for others to meddle with them.
But in precise terms, the Jeep Cherokee problems show this is not the case. Valasek and Miller discovered the problem, a security hole in the Sprint cellular connection to the UConnect infotainment system, not industry insiders. This is only the latest example of independent researchers finding flaws that catch the industry by surprise. Third-party researchers at Cal-San Diego and Washington were the first to show automakers there were cyber holes in their cars. Third-party researchers were the ones who found vulnerabilities in the Progressive Insurance "Snapshot" dongle. Now FCA's UConnect system.
Hopefully, Copyright Office officials have noted those distinctions. They're important ones, because industry officials have bristled at independent researchers both during and after May hearings on the copyright law. In a summary of a letter sent earlier this month to a Congressional committee investigating car hacking, the Auto Alliance, the industry's leading trade group, likened them to "technology pirates."
"Automakers are facing pressure from the organized efforts of technology pirates and anti-copyright groups to allow the circumvention of protection onboard networks, and to provide hackers with the right to attack vehicles carte blanche under the auspices of research," the Alliance wrote. Publicizing research results is another aspect of independent research that automakers oppose. They equate it to providing a blueprint for malicious hackers.
But at the same time, automakers have ignored past results when researchers withheld details of their work. While noting they withheld key details from their work to prevent a criminal copycat from following their trail, Valasek lamented such a lose-pose proposition. "If you don't show everyone your hand of cards, people dismiss it or question the actual research or results," said Valasek, director of vehicle security at IOActive. "So the best thing to do is get in the car and show them how it works, and hopefully cars become more secure after this."
More importantly, the public scrutiny of the results has ensured vulnerabilities get fixed. Would cars have been secured if independent researchers had been prohibited from doing their work? Probably not. In FCA's case, the company didn't even know about the vulnerabilities until Valasek and Miller alerted them back in October.

When the company held a conference call with federal safety officials on July 16, they merely intended to issue a technical service bulletin to advise dealers on how to fix the problem, according to a chronology of events filed with the National Highway Traffic Safety Administration. But when WIRED Magazine ran a story explaining the hack on July 21, federal officials took immediate notice. Under pressure from the government, FCA issued a recall two days later.
"The Homeland Security folks sent out broadcasts that, "Here's an issue that needs to be addressed," said Nathaniel Beuse, associate administrator at NHTSA. Elsewhere, Senators Ed Markey (D-MA) and Richard Blumenthal (D-CT) have introduced legislation to set minimum federal standards for automotive technology and have since urged NHTSA to investigate whether more recalls are needed.
None of that happens without Valasek and Miller's research.
A ruling from the Copyright Office may come in September or October. Should the Office permit the work of third-party researchers to continue, industry leaders have indicated they may take their fight against independent researchers to Congress.
In the meantime, they continue to downplay the valuable role of independent search. Earlier this month, when the industry announced the creation of a Information and Sharing Analysis Center that will evaluate cyber threats, an official emphasized they wanted to work with researchers in "controlled environments," which was a nice way of saying researchers willing to keep their results secret.
Five years into the hacking threat, automakers still don't get it. They're still months away from getting the ISAC operational and still more concerned about being embarrassed by security flaws than actually getting them fixed. In confronting a challenge they've proven ill-equipped to address, they're intent on chasing the best hopes they've got at solving the problem right out of the discussion.
Related Video:


Sign in to post
Please sign in to leave a comment.
Continue